Estimated reading time: 3 minutes
This past year has unfolded itself unlike any other to us as something we could have never predicted. Many organizations tend to plan for the unexpected, but very few were prepared for the global pandemic that shell-shocked this world. Very quickly employers were forced to furlough those that they could afford in order to keep moving swimmingly forward without suffering any losses, which has been rather unfortunate for many. Several employees have been allotted the opportunity to work from the comfort of their home offices to continue the operational flow. For many the new working ‘office life’ was proven to be quite difficult, for they were not able to manage the work-life-balance, but on the other hand, millions found their adjustment to be a successful switch-up. Remote workforces have been foreseen to be an effective and highly cost-efficient venture for enterprises and businesses of all sizes. Seemingly presenting itself as the ideal working environment, though it can be quite vulnerable to many dangerous outlets and even result in data breaches.
 Seeing as how homes are now identifying as the corporate network which employees are working off of, whether that be the Kitchen table, a quiet hall closet, or a makeshift bedroom/office environment, people are making it work so that they can successfully continue to do their jobs in a safe manner. Who knows how long this trend will stick around, but experts have predicted that it will become a new normal even after the virus has come and gone, post-vaccine administering. All of this being said, a work-from-home environment calls for an unintentional invitation for insecurities to flow in. These “offices” are no longer protected by the corporate firewalls that have been previously placed, so it’s up to obediently follow their organization’s defense strategy, knowing that a possibility for human error mistakes can potentially occur.
Seeing as how homes are now identifying as the corporate network which employees are working off of, whether that be the Kitchen table, a quiet hall closet, or a makeshift bedroom/office environment, people are making it work so that they can successfully continue to do their jobs in a safe manner. Who knows how long this trend will stick around, but experts have predicted that it will become a new normal even after the virus has come and gone, post-vaccine administering. All of this being said, a work-from-home environment calls for an unintentional invitation for insecurities to flow in. These “offices” are no longer protected by the corporate firewalls that have been previously placed, so it’s up to obediently follow their organization’s defense strategy, knowing that a possibility for human error mistakes can potentially occur.
Through the use of Virtual Private Networks (VPNs) and other remote working platforms, employees can gain access to the company’s infrastructure and files while working away from their central office space. This is extremely critical when it comes to the shared Wi-Fi network that the user could be linked to. IT managers should be able to yield any complaints or questions coming from workers to help answer their questions and get the workplace functioning in a swifter manner. It should be known that companies that employ part-time and full-time employees from other parts of the globe may instill precautions to limit security risks. To help reduce additional remote working risks, employees will need to listen to all the advice that comes along with using VPNs, researching Anti-Malware, regularly updating their devices to ensure that the hardware and software are functioning properly for the Monday-Friday 9-5 workday.
BlueStar’s Remote Worker-Student Solutions Guide
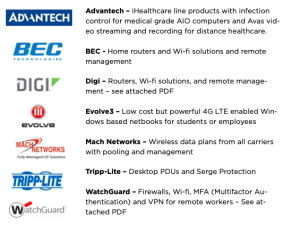 During these unprecedented times BlueStar has created a portfolio of solutions for remote employees and students that can help companies, schools, and healthcare organizations provide secure access for remote individuals and a safe environment for frontline healthcare workers. From connectivity to security, devices, and peripherals we have products to help individuals working remotely.
During these unprecedented times BlueStar has created a portfolio of solutions for remote employees and students that can help companies, schools, and healthcare organizations provide secure access for remote individuals and a safe environment for frontline healthcare workers. From connectivity to security, devices, and peripherals we have products to help individuals working remotely.
Speaking of the 9-5, many employees have recorded working more hours at home, than they would have commuting to their office space. Yes, workers can say they’ve dissolved their commute times entirely, but they are spending more time behind the screen of their computers to put in an additional amount of work into the shift. There’s an opportunity here for people to move past the mundane parts of a typical shift, freeing themselves up from the bad habits, down time, and inefficient processes, from ineffective meetings that could be summarized entirely in emails and cut out all of the unnecessary bureaucracy, creating a better workplace for all.
There are many resources employees and employers both can utilize to better frame out their workplace from a secure and safe standpoint. This mindset depends entirely on the organization and the practices they have put in place for their workers to adopt. At the same time, employees will need to consider that when working from home, their own devices and tools can help them work better, for example, home security systems and Wi-Fi connections come into thought processes. These technical systems can help users deter criminals and offer protections from data breach damage that can occur thanks to the work stealthy work of cybercriminals.

